Mission Control Blog
Discover how to advance your security program with the latest content from our community.

In 2020, average time to remediate a vulnerability was 171 days. Today it's 252 — and AI just collapsed time-to-exploit to nine hours. A long-form argument that the V
- Vuln Mgmt
- CTEM
- CAASM
- SecOps

AI agents authenticate as service accounts but reason like employees — and most security teams can't see the difference. Here's why JupiterOne built AI Attack Surface
- AI ASM
- IAM
- CAASM
- SecOps

Today we're launching the new JupiterOne — a refreshed AI Risk Management Platform plus two products our customers asked us to build: AI Attack Surface Management and
- AI ASM
- Vuln Mgmt
- CCM
- CAASM

Anthropic's Project Glasswing has shown that AI can now chain together vulnerabilities and exploit software faster than almost any human. That changes everything.
.png)
Learn what RSAC 2026 reveals about the AI accuracy gap in security — and why agentic platforms without a knowledge graph add risk faster than they reduce it.
- CAASM
- CSPM
- CCM

Cyberattack reveals control-plane risk and how graph-native visibility helps security teams map attack paths and blast radius before an incident strikes.
- CAASM
- Vuln Mgmt

Discover how AI compliance automation is making continuous controls monitoring accessible to every team member
- CCM
- CAASM

JupiterOne's new integration with Upwind brings runtime CNAPP data into the asset graph
- CAASM
- CSPM
- CNAPP

Most security teams can see their cloud but not what's behind the firewall. Learn how the JupiterOne Collector bridges on-prem visibility into your security graph.
- CAASM
- CCM

As acquisition activity continues across the security market, teams are reassessing their CAASM foundations- & future-proofing their visibility strategy.
JupiterOne just got a fresh new look. Our refreshed design brings clarity, consistency and a modern design language.
- CAASM
- CTEM
- CSPM
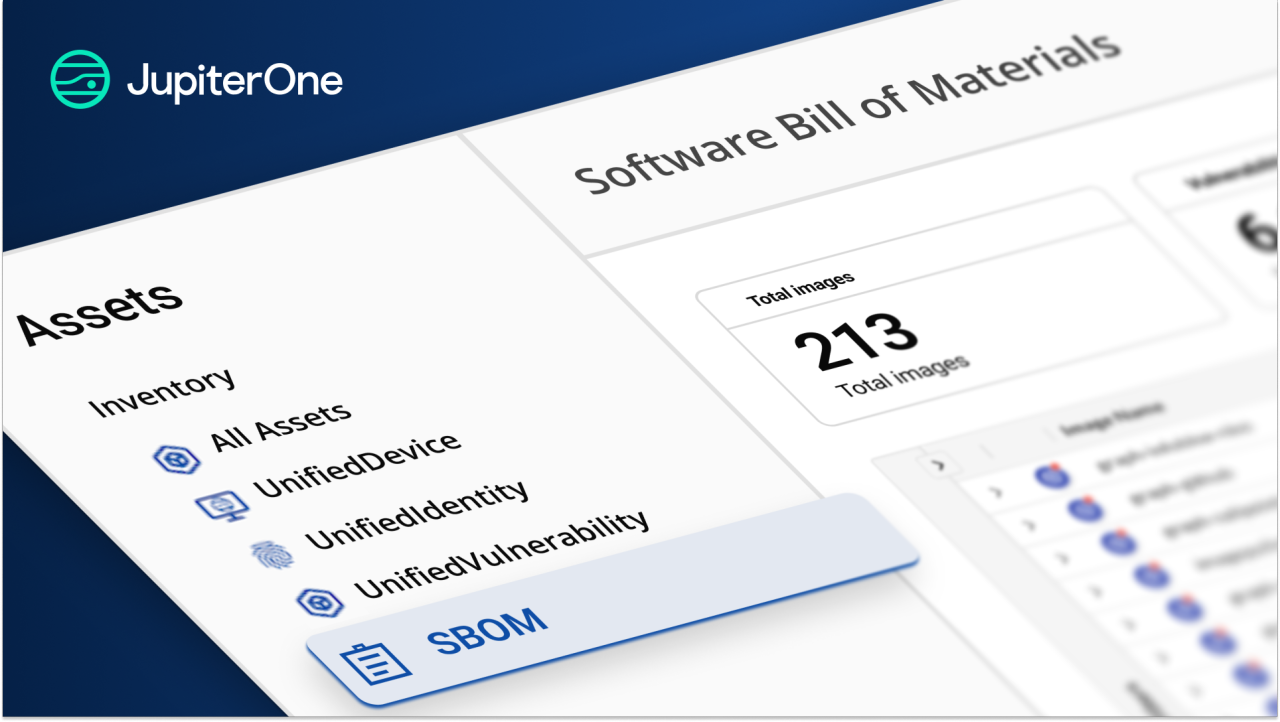
JupiterOne turns SBOMs into living intelligence—automated, enriched, and actionable to cut software supply chain risk fast.
- VulnMgmt
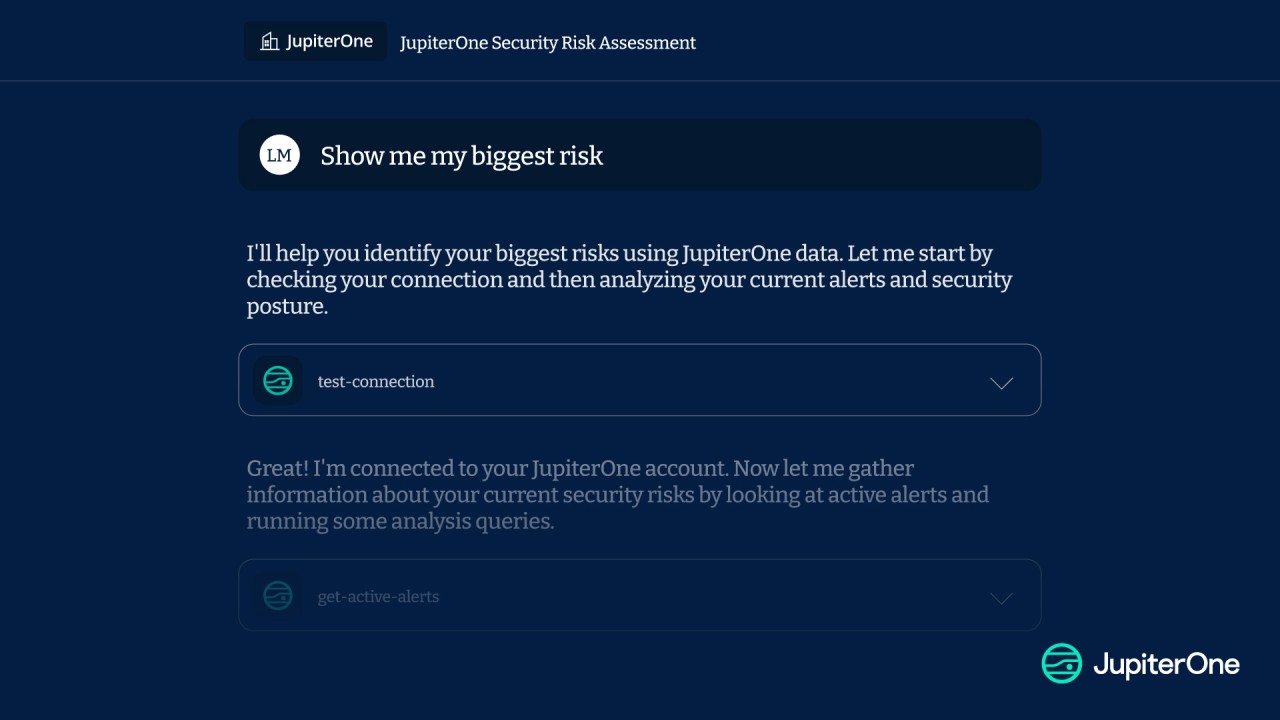
Discover 5 key tips for using JupiterOne MCP to automate risk insights, build dashboards, and streamline security with natural language prompts.
- CAASM
- VulnMgmt
The JupiterOne MCP Server helps security teams operationalize agentic AI—connecting models to live context, tools, and data without rebuilding your stack.
- CAASM
- SecOps
- Vuln Mgmt

New Kubernetes Rule Pack covers more CIS controls for Namespace and Secrets Management
- CAASM
- CSPM

New Kubernetes Rule Pack covers 26 CIS controls for RBAC & Pod Security
- CAASM
- CSPM

Legacy IAM falls short. Identity first security uses continuous, contextual access controls to protect a decentralized world—far beyond the old perimeter.
- CAASM
- IAM
- CSPM

Unify cloud risk insights and asset context to prioritize and remediate vulnerabilities faster with the Orca Security and JupiterOne integration.
- CAASM
- VulnMgmt
- CSPM

Discover 5 essential cybersecurity risk assessment frameworks to protect your digital assets. Learn their benefits, key features, and how to choose the right one
- CAASM
- VulnMgmt
- CSPM

The new Widget Editor delivers a more intuitive experience. Edit widgets in place, declutter your workspace, and get insights faster.
- CAASM
- CTEM
- SecOps

Streamline security with JupiterOne and Jira. Automate issues, enhance collaboration, and track risks to boost efficiency and response times.
- CAASM

Unified Device creates a cohesive view of assets with advanced correlation and self-healing for simplified, actionable security insights.
- CAASM
- SecOps

Discover JupiterOne's 2024 milestones! From upgrading our Security Graph for faster insights to launching features like CTEM, CCM, Unified Device, and Rule Packs.
- CAASM
- CTEM
- CCM

Unlock proactive IAM security with Okta and JupiterOne, gaining real-time insights, enforcing least privilege, and reducing risks in dynamic cloud environments.
- IAM
- CAASM

Explore Gartner's latest report on Exposure Management and learn how your organization can prioritize vulnerabilities and minimize exposures.
- CTEM
- Vuln Mgmt

Discover how Cyber Asset Attack Surface Management (CAASM) is providing enhanced visibility of internal and external assets in 2025.
- CAASM
- SecOps

CCM delivers real-time visibility, proactive risk management, and streamlined compliance for security.
- Compliance
- CCM

Explore JupiterOne’s Public Postman Workspace to streamline your workflows and enhance your security operations.
- CAASM

Vulnerability scanners flood teams with alerts, but CTEM helps prioritize based on exploitability and business impact, ensuring focus on the most critical threats.
- CTEM
- Vuln Mgmt

Learn how CTEM helps organizations reduce their attack surface, protect valuable assets, and stay ahead of attackers. Download our white paper to get started with CTE
- CTEM
- Vuln Mgmt

It’s Cybersecurity Awareness Month, but before you send out those animated videos and "helpful" phishing tips, take a hard look at your own practices.

JupiterOne helps organizations manage cloud permissions and prevent privilege escalation across AWS, Azure, and Google Cloud.
- CAASM
- IAM
- CSPM

There is a lot of confusion out there when it comes to cloud native IT and cloud security tools. Things have gotten rather complicated over the last few years as we
- CSPM
- CAASM
- CTEM

A CISO's Top 6 Takeaways From the Cyentia Institute’s Inaugural Study of EPSS Data and Performance "A Visual Exploration of Exploitation in the Wild"
- CTEM
- Vuln Mgmt

Here’s how Fleet integrates with JupiterOne to gain comprehensive insights and enhance the security in our environment.
- GRC
- Vuln Mgmt

Today, we’ll dig deeper into attack surface management and explore the benefits and differences across CAASM and EASM
- CAASM
- EASM
- SecOps
- ASM
- CTEM

Discover how Gartner's latest report on Attack Surface Management can help your organization enhance cybersecurity with proactive measures and asset visibility.
- CAASM
- CTEM

Discover how graph databases revolutionize threat detection in cybersecurity, enhancing visibility, risk management, and proactive security operations with JupiterOne
- Vuln Mgmt
- SecOps

Comparing Cloud Security Posture Management to Cyber Asset Attack Surface Management
- CAASM
- CSPM

Discover how CAASM and IAM can reduce security risks from over privileged accounts and inefficient user deprovisioning.
- IAM
- CAASM

CAASM empowers proactive defense by integrating internal insights and external threat visibility, enabling prioritization of critical cybersecurity risks.
- CAASM
- CTEM

Discover how JupiterOne addresses critical vulnerabilities with asset inventory, relationship mapping, and actionable insights for enhanced security.
- Vuln Mgmt

Introducing Continuous Threat Exposure Management (CTEM) with JupiterOne and WatchTowr: A Proactive Approach to Cybersecurity
- CTEM

Organizations are transitioning to the cloud faster than ever to keep up with the changing consumer and business climate. According to Gartner, by 2023, 40% of all
- CSPM
- CAASM

JupiterOne aggregates and normalizes data from hundreds of different sources so you can identify and triage security risks easily.

It seems like a simple question. “Are any of our deployed user endpoint devices missing an endpoint detection and response agent?”

At the most basic level of the Incident Response Hierarchy, security teams must know the assets they are defending.
- CAASM

Natural language search leverages AI to bring ease of use to the forefront of the JupiterOne platform.

Here’s our recap of Black Hat, BSides and DEFCON, otherwise known as Hacker Summer Camp 2023!

As companies move to the cloud, continuous compliance efforts - which may feel like an obstacle - can become an accelerator in the migration process.
- GRC

It's more likely today that cloud-enabled businesses need to pay attention to compliance frameworks like SOC 2 to protect themselves and their customers.
- GRC

JupiterOne is releasing new functionality to better support customers' hybrid and on-premises devices and infrastructure along with new AI-powered search options.

Explore related assets, segment your data, and drill into your AWS environment with JupiterOne to get prescriptive with alerts and remediation.

Discover how the Jamf integration for JupiterOne enriches visibility with Mac device information and ownership.

Cyber asset management is vital to a secure and resilient digital infrastructure. Learn about its top challenges and how to overcome them.
- CAASM

Learn how these similar but different solutions can work together and create a more cyber-resilient environment.
- CAASM

Finding the right cyber asset management solution takes work. Ask these five questions to find the solution that's fit for your business.
- CAASM

Attack surface management and vulnerability management often overlap but are both vital to an organization’s cybersecurity posture.
- CAASM
- Vuln Mgmt

JupiterOne VP of Marketing Rebecca Sanda shares her story behind becoming an LGBTQ Ally and the inclusive employee culture at JupiterOne.

When are Data Security Posture Management tools useful and how can JupiterOne be used for basic DSPM functions?

Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.
- This is some text inside of a div block.
- This is some text inside of a div block.
- This is some text inside of a div block.
- This is some text inside of a div block.
- This is some text inside of a div block.