Resources
Get the latest thoughts from analysts and JupiterOne Champions on how to level up your security program.

See how JupiterOne replaced manual screenshots and spreadsheets with query-backed SOC 2 Type 2 evidence from AWS, GitHub, and Google Workspace.

Cut audit prep time from months to days and achieve continuous compliance with real customer-proven results.
- Compliance
- CAASM

Discover how EagleView streamlined cloud security, improved identity risk management, and boosted cybersecurity maturity by 150% using JupiterOne’s CAASM platform.
- CAASM
- CSPM

Mirriad improved security, compliance, and efficiency with JupiterOne, gaining real-time visibility and automation to scale with top media partners.
- CAASM
- Asset Management
- Vuln Management

Learn how Socotra used JupiterOne to achieve full asset visibility, streamline compliance, and secure operations during rapid growth and expansion.
- CAASM
- Compliance

An American financial services company achieves collaborative vulnerability management and asset management that actually works, using a risk-based approach to managing its asset ecosystem with a centralized view of its environment.
- Vuln Mgmt

Learn how Okta has turned security into a business enabler by bringing secure-by-design products to market quickly.
- IAM
- CAASM

Mercury Financial established complete cyber asset visibility across 130 integrations within one week.
- GRC
- CAASM
- Vuln Mgmt

With JupiterOne, Indeed gained a holistic view of all its asset relationships and attack surface alongside a broad cloud migration.
- CAASM
- Vuln Mgmt
- CSPM
- IR

Learn how LiveIntent uses JupiterOne daily to secure thousands of ephemeral devices and a highly dynamic workload in AWS.
- IR

See how Blend simplified a major acquisition, cyber asset management, and continuous compliance with the JupiterOne platform.
- CSPM

Auth0 achieved end-to-end cloud security. monitoring and a complete understanding of 3rd party risks using JupiterOne.
- SecOps
- IAM
- Vuln Mgmt

Learn how Codoxo became healthcare compliant in two months at a price point suitable to its business size and resources.
- GRC

Databricks deployed JupiterOne and started discovering critical data within an hour of deployment.
- IR
- Vuln Mgmt

Aver drastically reduced the time and effort to assemble detailed attack surface reports and complete post-breach analysis.
- CAASM

Fragmented ownership and limited asset visibility are the top barriers to DORA compliance. Gartner outlines how cybersecurity leaders can embed real-time monitoring,
- CCM
- AI ASM
- CAASM

Gartner® latest report provides strategies to prioritize vulnerabilities and reduce exposures.
- CTEM
- Vuln Mgmt

Learn how JupiterOne's CTEM solution enhances cybersecurity with asset visibility, attack surface discovery, exposure prioritization, and automated responses.

Cyentia's "A Visual Exploration of Exploitation in the Wild" study covers insights for using EPSS data to manage and prioritize vulnerabilities in your environment.
- CTEM

The 2023 State of Cyber Assets Report revealed nearly 600% annual growth in vulnerable cloud attack surface and 133% growth in cyber assets over the 2022 report.

It’s not enough to "know" where all your assets are. Gaining ‘visibility’ when you don’t have the ability to act on it is pointless. Download this whitepaper to learn
- CAASM

In this paper from the JupiterOne research and development and data science teams, we'll discuss the early findings from our ongoing attack surface research, pose ope
- CAASM

JupiterOne commissioned Forrester Consulting to conduct a Total Economic Impact™ (TEI) study and examine the potential return on investment (ROI) enterprises may real
- SecOps
- CAASM
- CSPM
- IR

This 30 page research report details key cybersecurity coverage gaps and how organizations plan to improve their security posture. Download using the form below.
- CAASM
- SecOps

In this first-ever SCAR report, we analyzed over 370 million cyber assets, findings, and policies across almost 1,300 organizations to better understand today’s cyber
- CAASM
.png)
Learn how security teams use JupiterOne to map ICT assets, close control gaps and meet DORA's operational resilience requirements faster.
- CCM
- CAASM
- AI ASM
Ephemeral infrastructure broke traditional compliance. Here's how Continuous Controls Monitoring rebuilds it — continuous, automated, and proven against live data.
- CCM

JupiterOne has partnered up with BreakFree Solutions, a leading provider of practical cloud, DevOps, and automation professional services to enterprise organizations.
- SecOps

These 6 steps and tactics will move you into the fast-lane when it comes to delivering better products by helping you create a DevSecOps culture.
- SecOps

Efficient security operations and prompt detection of breaches are critical for limiting the impact bad actors can have on your business. Download our ebook and learn
- CAASM

Whether you invest in tools to automate and accelerate the security review process or you do it manually, these 8 plays will help you methodically create and submit
- SecOps

In this workbook, we dive into each area to ensure your team is prepared for proactive security using a DevSecOps mindset. Then, our blueprint will help set the found
- SecOps

If one bad apple can spoil the entire bunch, do you analyze a subset of the bunch to find the bad apple, or do you look across the whole population? How might this
- SecOps

The digital age forced an evolution of the term "asset." Physical assets still exist, but cloud and digital transformation added complexity that extends beyond the
- CAASM

Enrique Salem, Partner at Bain Capital and JupiterOne CEO Erkang Zheng discuss best practices to approaching cybersecurity at board meetings based on years of experie
- SecOps

This collection of stories from experienced security leaders and practitioners details the major business problems they experienced when implementing cybersecurity
- CAASM
- SecOps

In this collection of stories, 19 cybersecurity experts offer a unique look at cybersecurity that addresses the technical, interpersonal, and strategic aspects of th
- CAASM
- SecOps
- CSPM

Written by Sounil Yu, and with forewords by security industry luminaries Dan Geer and Wendy Nather, the Cyber Defense Matrix eBook helps practitioners, vendors, and
- SecOps
- CAASM
- CSPM
This session is designed for security practitioners who own or support compliance outcomes: the engineers and architects who configure technical controls.
- CCM

Unified assets are the foundation of a strong security posture and getting the most from them is easier than you think.
- CAASM
Join us for a preview of JupiterOne Workflow Automation, a new capability that transforms your security insights into automated action.
- CAASM
- CCM

Eliminate on-prem blind spots. See how the JupiterOne Collector unifies data center, legacy, cloud, and SaaS assets—plus a live demo and hybrid compliance use cases.

Learn how to transform security validation from manual quarterly checks into continuous automated testing using J1QL queries against your cyber asset graph.
- CCM

Unlock the full potential of JupiterOne with some of our favorite out-of-the-box managed dashboards and our ready-made query library.
Master JupiterOne's Python SDK to automate security workflows, scale J1QL queries, and build custom integrations beyond the UI. For power users & developers.
- CAASM
In today's economic environment, cutting costs without compromising performance or security is a top priority for cloud-driven organizations.

Join us for What's New in JupiterOne: July Edition to explore the latest features, updates, and enhancements to maximize your platform value.
Stay ahead in cyber asset security—join our webinar for a deep dive into J1QL, JupiterOne’s powerful query language for graph-based data insights.

Join us for What's New in JupiterOne: June Edition to explore the latest features, updates, and enhancements to maximize your platform value.

Explore how to detect risky AWS trust relationships using JupiterOne’s Insights, Questions & Alerts in this 45-min focused webinar.
Explore JupiterOne Alerts: overview, configuration tips, and a live demo of using Alert Rules to streamline vulnerability discovery and triage.
Learn to use JupiterOne’s UI, dashboards, and automation—no J1QL expertise needed. Get insights fast with built-in tools and zero coding.

Learn how CAASM helps prevent privilege risks by mapping cloud permissions, roles, and misconfigs across dynamic environments.

Gain full asset visibility to streamline device management, improve hygiene, and close critical security gaps.
Use JupiterOne MCP Server to turn natural language into insights and unify your security data—no coding required.

Sean Catlett and James Mountifield look at how organizations migrating to the cloud can use continuous compliance as an accelerator to the process.
- GRC
See your attack surface the way attackers do. JupiterOne AI ASM continuously discovers exposed assets and surfaces real risk in plain language.
- AI ASM
- CTEM
One view across every scanner, cloud, and code repo. UVM unifies vulnerability data with asset context so you fix what matters first.
- UVM
- CTEM

See how CCM unifies asset visibility, automates control testing and detects configuration drift—so you can prioritize remediation based on real-time posture data.
- CCM
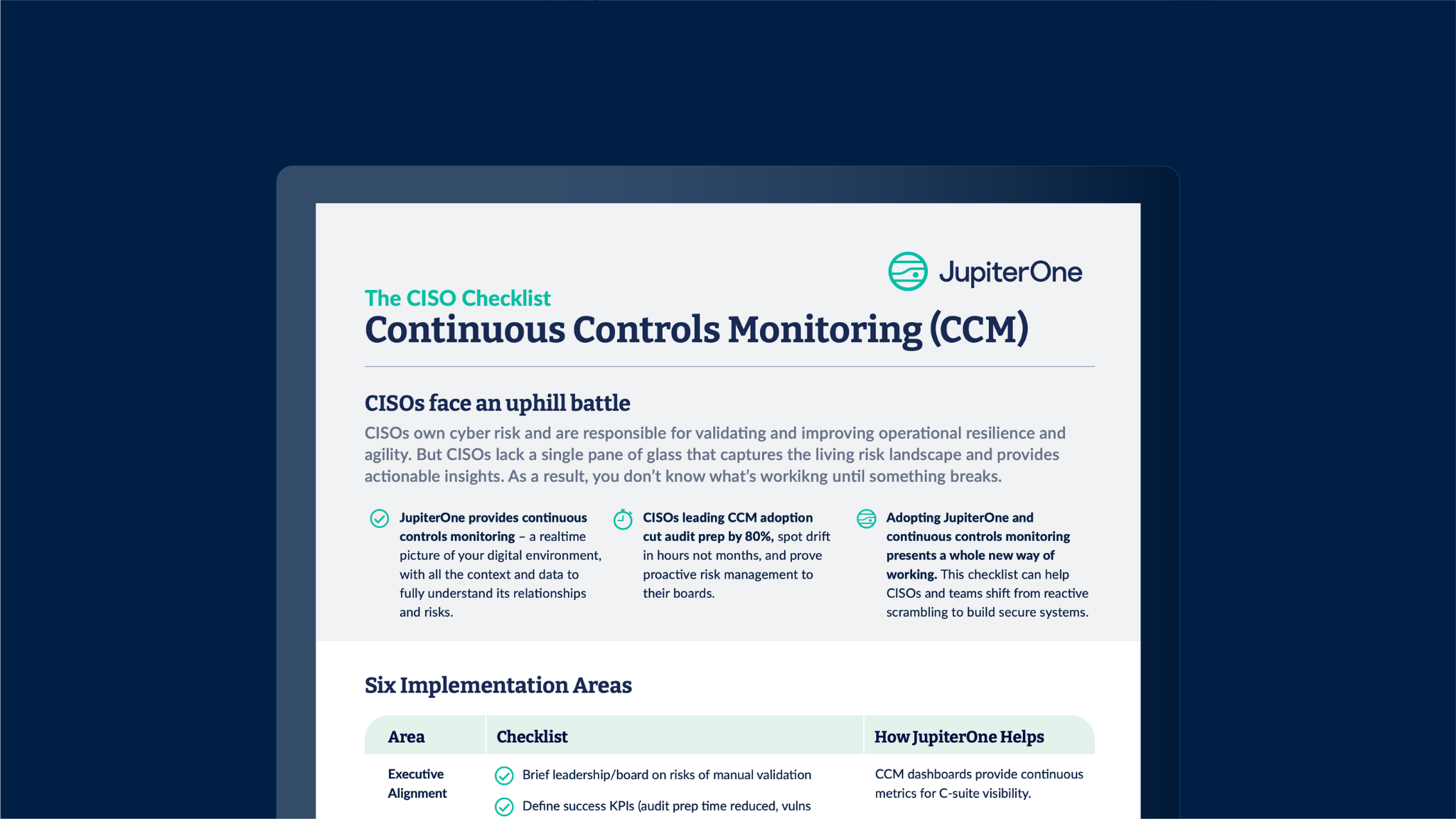
A before-and-after comparison showing how CCM transforms fragmented visibility and manual evidence collection into unified, automated control validation.
- CCM

Automate control validation across your entire environment with executable queries against a unified asset graph.
- CCM
- CAAM

Discover the most critical and exploitable vulnerabilities, prioritize with asset context based on business impact and receive a recommended remediation plan.
- CTEM

A unified view of all cyber assets, across cloud, on-premises and hybrid environments. Map and visualize asset relationships to see vulnerabilities and their impact.
- CAASM

Getting the answers to key questions is one of the greatest challenges facing security, IT, and DevOps teams today. These questions can be answered using JupiterOne.
- CAASM
- SecOps
- GRC
- Vuln Mgmt
- IR

Learn how to put in place real security for your AWS environment, with minimal resources, to protect the confidentiality, integrity, availability and privacy
- SecOps

It’s not enough to "know" where all your assets are. Gaining ‘visibility’ when you don’t have the ability to act on it is pointless. Download this whitepaper to learn
- CAASM

Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.
- This is some text inside of a div block.
- This is some text inside of a div block.
- This is some text inside of a div block.
- This is some text inside of a div block.
- This is some text inside of a div block.