Cloud Security Posture Management
Actionable context into cloud risks
Get better visibility across all your cloud environments. Discover and map all cloud resources, understand asset relationships, and quickly identify, prioritize, and remediate critical risks.
Get a Demo


Cloud Service Provider Integrations




Why is asset visibility important for cloud security?
Security teams cannot protect all their assets without visibility into their entire attack surface
Although CSPM tools provide great information into cloud environments, they only cover one piece of an attack surface. As a result, security teams can’t see how incidents connect to the rest of their assets.
As a result, teams experience:
How It Works

All from a single platform
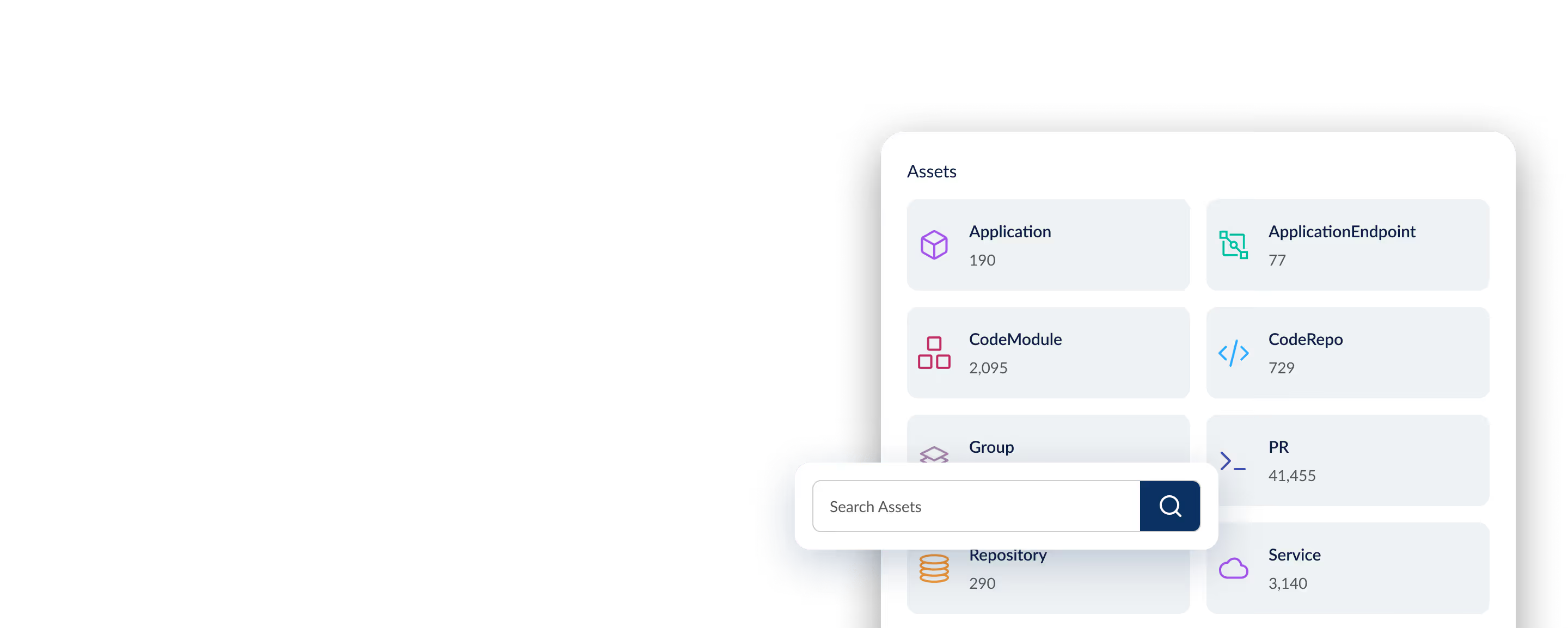
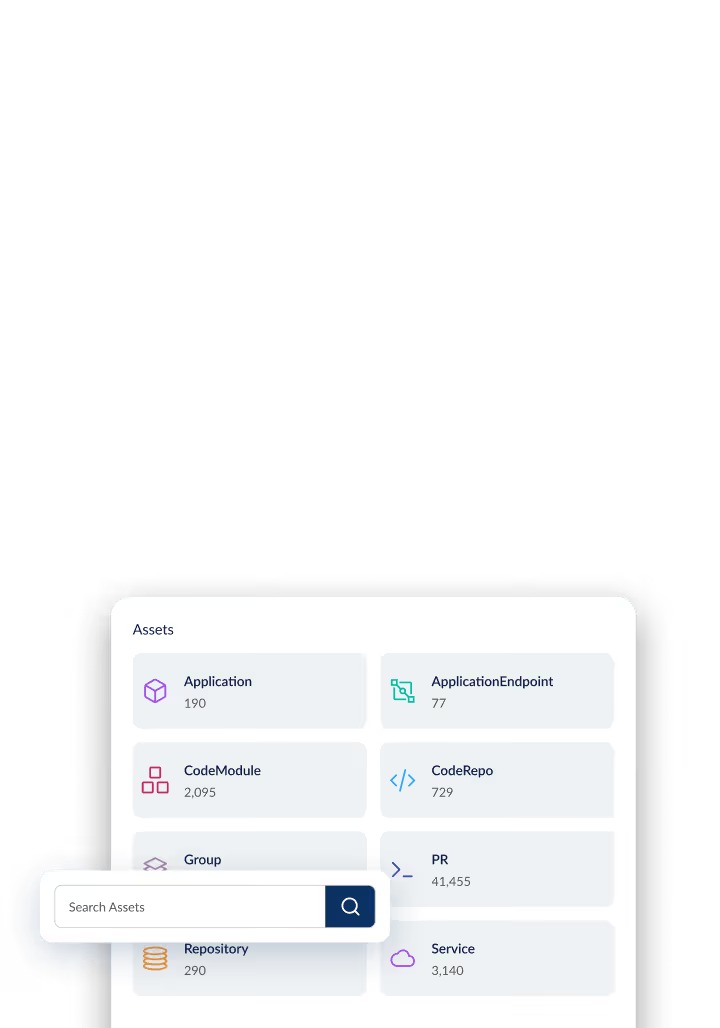
Unified Visibility
Achieve visibility across your entire infrastructure. Cloud service providers. Plus devices, code repos, users, and more.

Monitor attack surface
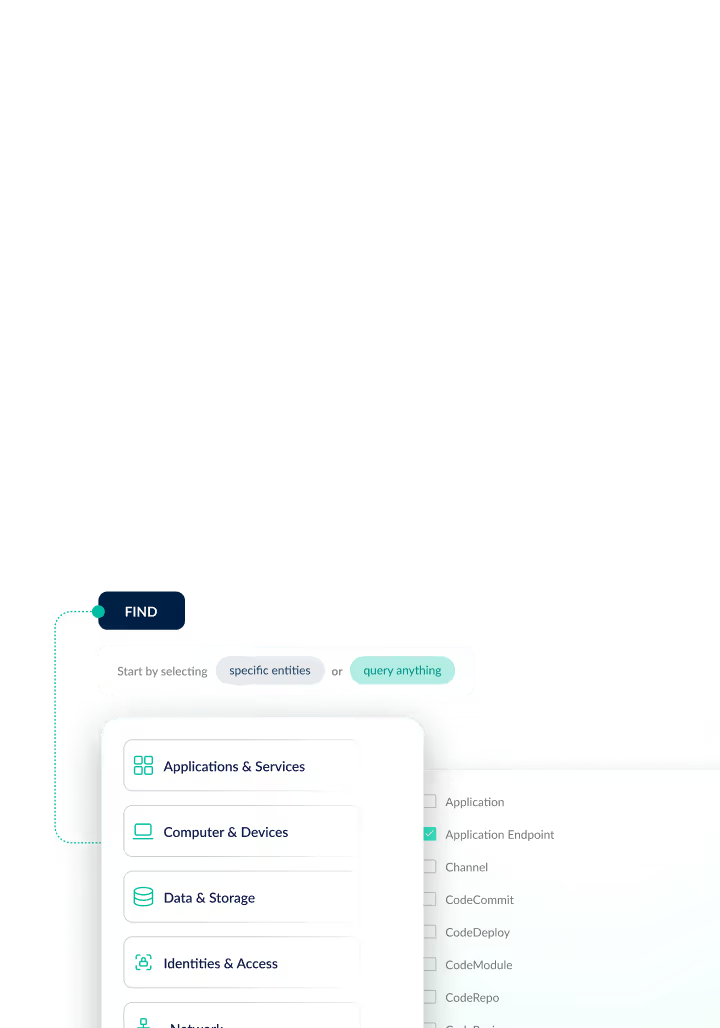
See Asset Relationships
Quickly analyze your assets. See the blast radius of security incidents. Identify security gaps and compliance gaps.

Remediate faster
Secure Your Attack Surface
Prioritize risks based on potential impact on your critical assets. Auto-send remediation steps directly to teams.
Benefits
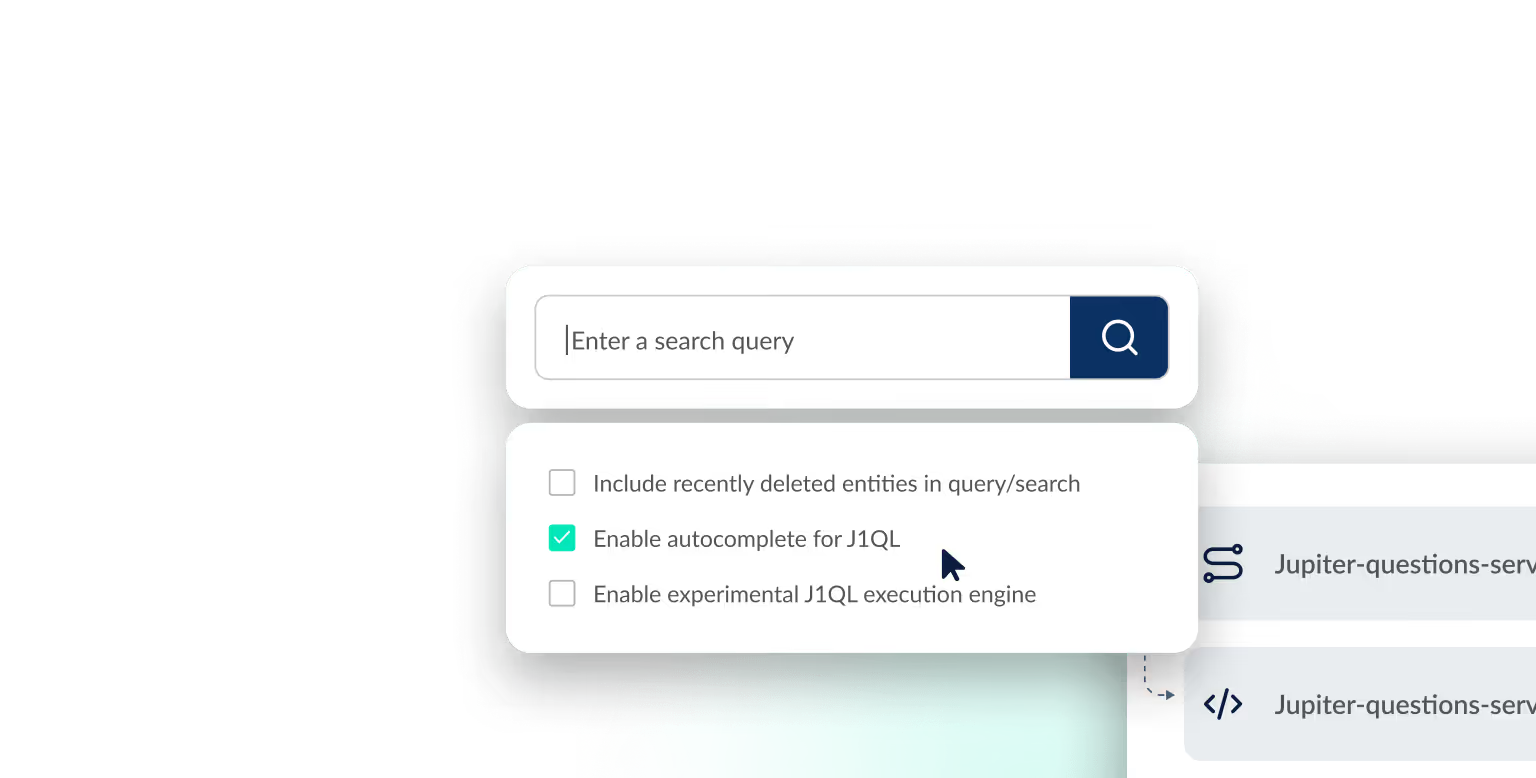
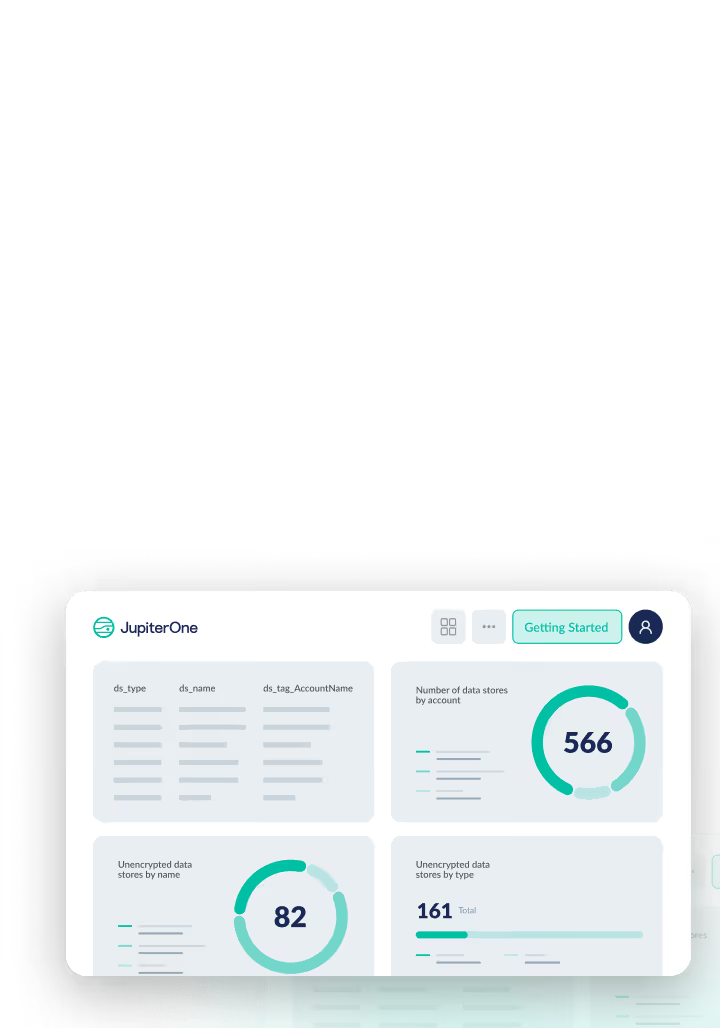
Simplify complex cloud environments
JupiterOne consolidates and normalizes asset data across complex, multi-cloud environments. Run a single query to search for information from multiple cloud providers, applications, and services. Eliminate hours of manual effort and get a holistic view of your cyber assets and cloud security posture.
Connect cloud assets to your cyber universe
JupiterOne offers complete coverage for all of your cloud entities. We connect the dots between assets, users, endpoints, code repos, and more to give your teams a full understanding of their environments.
Eliminate cloud resource misconfigurations & risk
JupiterOne automatically creates and classifies resource entries to continuously assess, audit, and evaluate configurations of your cloud resources. We detect compliance drift and reduce overall risk for your cloud-native efforts.
Control overly permissive access rights to your cloud
Manage permission reviews of identities within your organization with pre-defined access policies, rules, and alerting. Control everything from new and former employee accounts, partners, and third-party access with JupiterOne.
Leverage built-in automation, benchmarks, and policies
Maintain continuous compliance and meet the highest industry standards with pre-built frameworks including CIS Benchmarks, NIST, SOC 2, PCI DSS, and more. Automate security workflows with intelligent rules and alerts. Trigger ticket creation, communications, and actions to help you discover new issues.





Integrations


This is the most visionary tool on the market. It easily integrates with our tools. I don’t need 5 people to run it (unlike other pieces of software).
Neil F.
Security and Audit Manager


Fantastic automated solution for compliance and cybersecurity posture. JupiterOne cuts down the work for evidence submission for audits by 80%.
Syed K.
Security and Audit Manager


JupiterOne makes it possible for anyone to maintain compliance with SOC, PCI, HIPAA, and more. Really comprehensive solution!
Jasmine H.
Security