Security at the speed of AI
Get better visibility of all your cloud, AI, and on-premises assets. Visualize asset connections to see vulnerabilities and their blast radius. Get alerts when important changes occur. Automate compliance and audit evidence collection.







See what our clients have to say
Hear from the security teams using the JupiterOne AI Risk Management Platform to discover AI assets, assess risk and govern every model and agent continually, at enterprise scale.

"From a merger/acquisition perspective, JupiterOne was invaluable. As M&A activities in cloud native companies become increasingly popular, there is no better way to identify and tag assets than using a tool like JupiterOne."
Information Security Officer
•
Blend

"My role is to bring secure-by-design products to market quickly. JupiterOne's asset tracking and compliance automation is core to how I execute on that."
Cloud Security Engineer
•
Mercury Financial

"It's an example of a modern security product company that actually solves real customer problems. Asset management is something we security folks waved our hands about for too long. The graph is a security primitive you build your program on."
CISO
•
Rippling

"With the cost savings from identifying and de-provisioning orphaned AWS resources and not having to purchase separate tools, we've more than recouped our investment in JupiterOne!"
Manager, DevSecOps
•
Socotra
Discover how our platform works in 3 easy steps
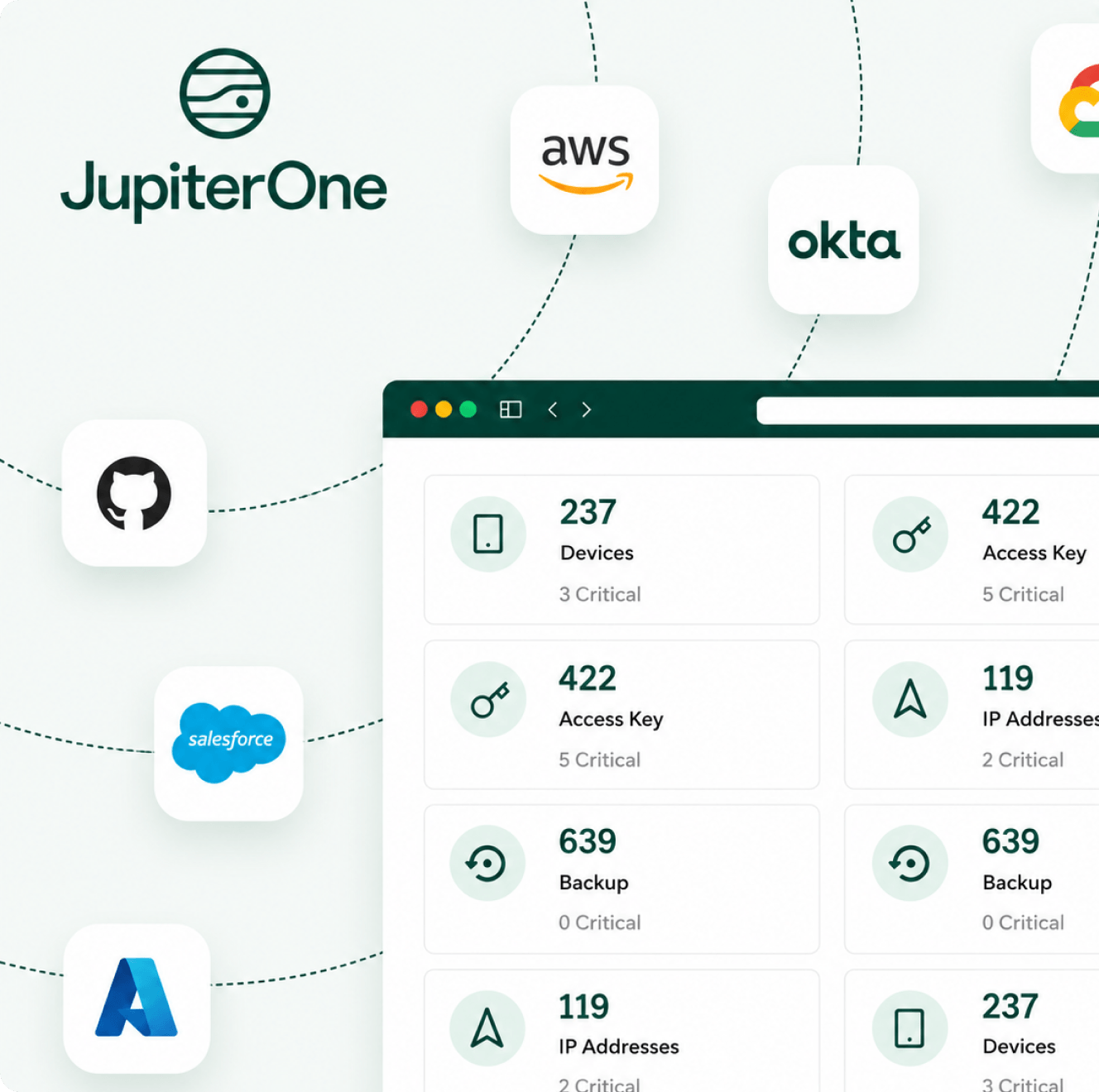
Collect and normalize asset data
Connect with all your security and infrastructure tools. 200+ integrations bring visibility into your cloud and on-premises assets.
Collect and normalize asset data
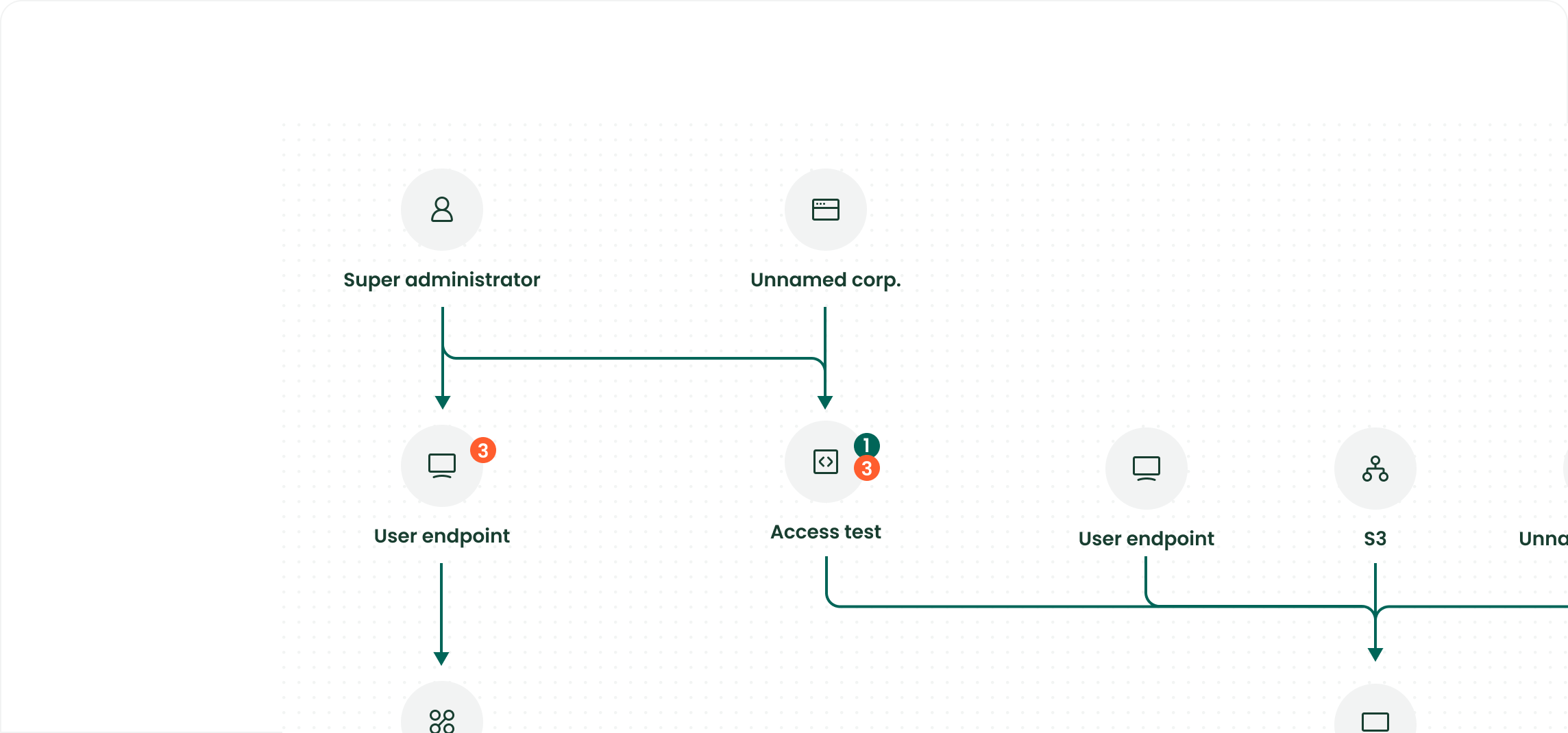
Map out assets and relationships
Automatically reveal unmonitored assets and map relationships to uncover gaps and risks.
Map out assets and relationships
Total Visibility
Understand your entire attack surface to swiftly identify, prioritize, and remediate critical issues and vulnerabilities.
Total Visibility
All you need in one platform
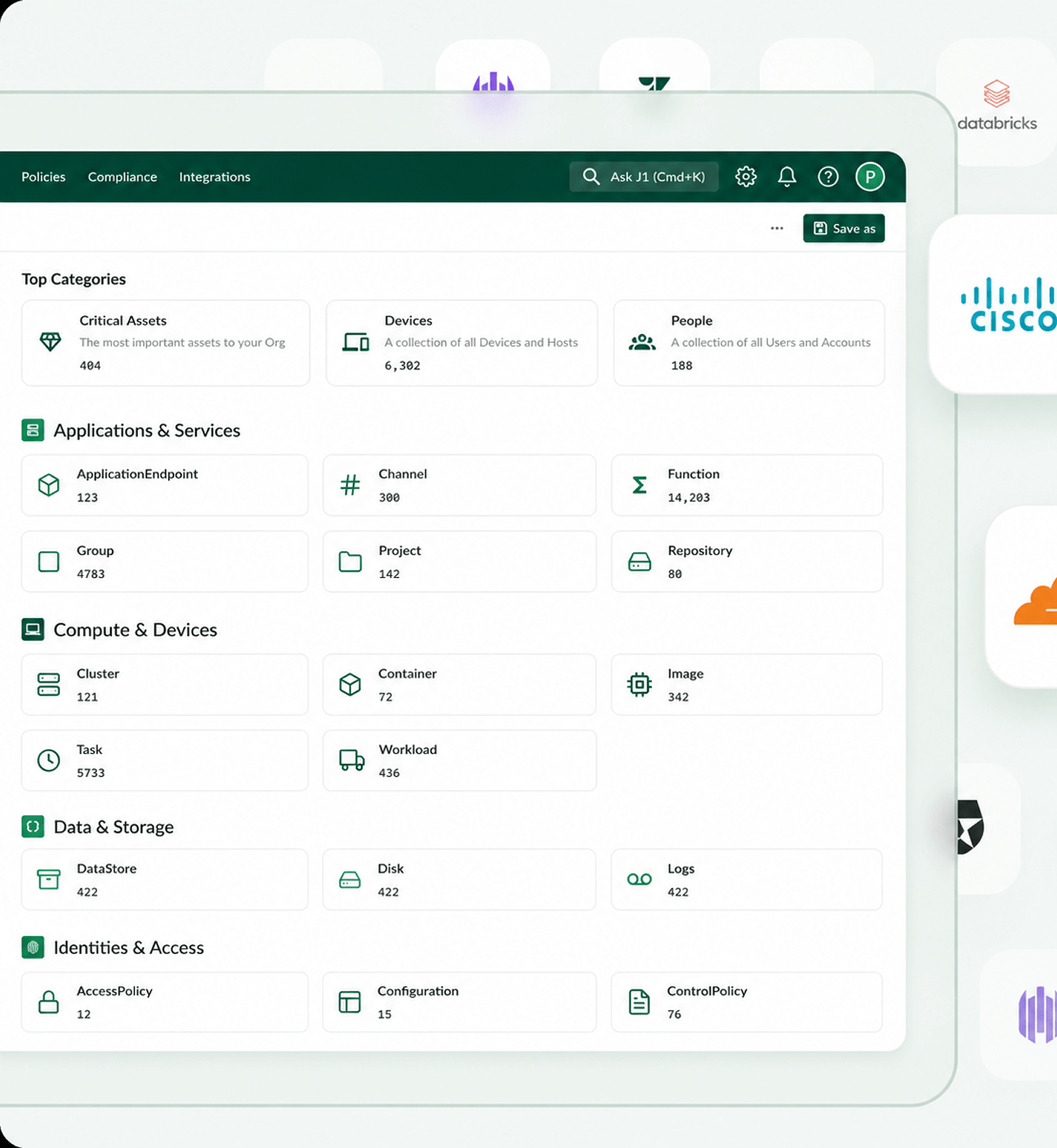
Collect and normalize assets
API driven, agent-less collection of all assets across your tech stack. Consolidate asset data from IT, DevOps, security, HR, and other tools into a single source of truth.
Plus, see data from vulnerability scanners, security controls (like cryptographic keys), and other valuable context into the security state of assets.
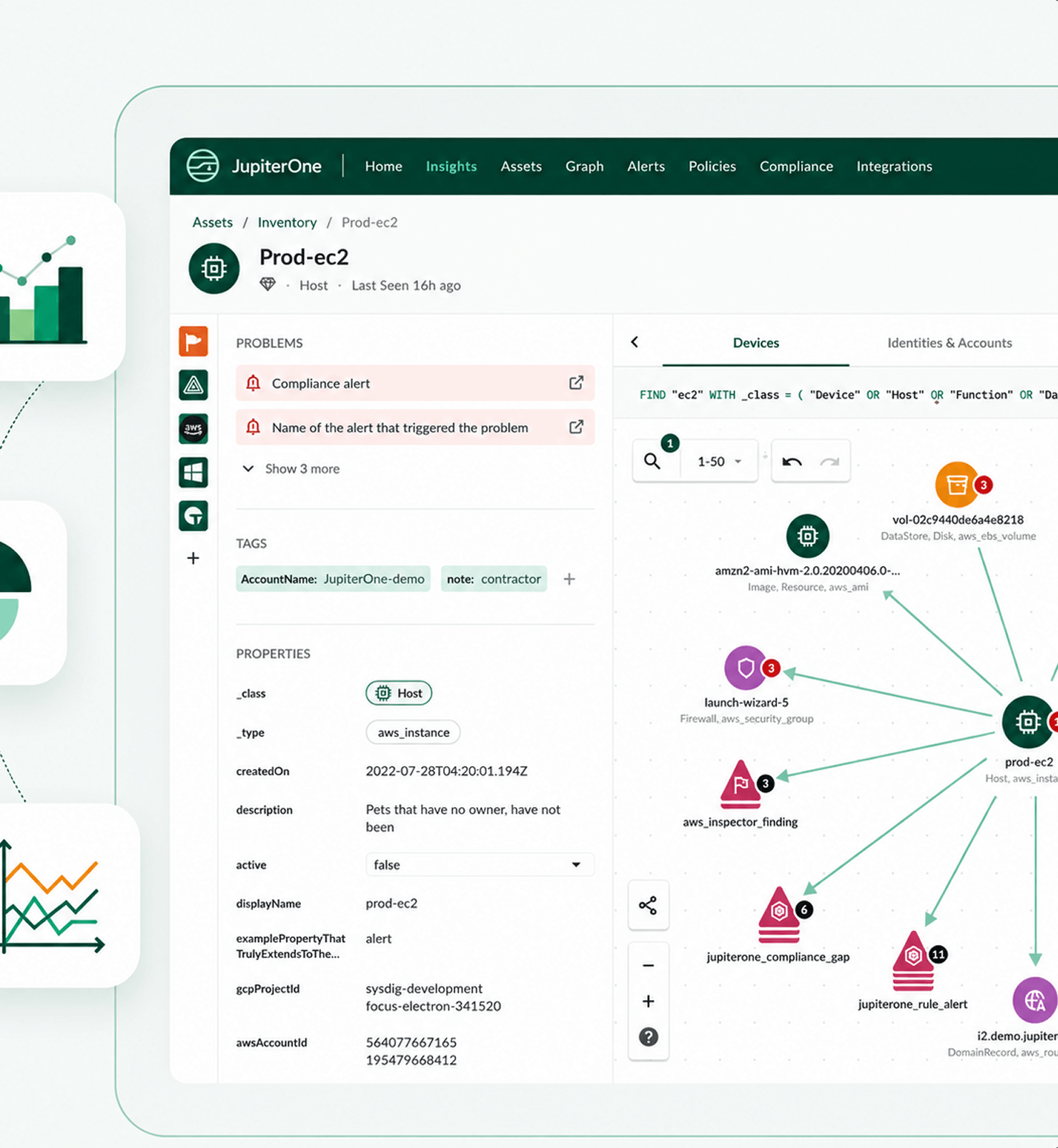
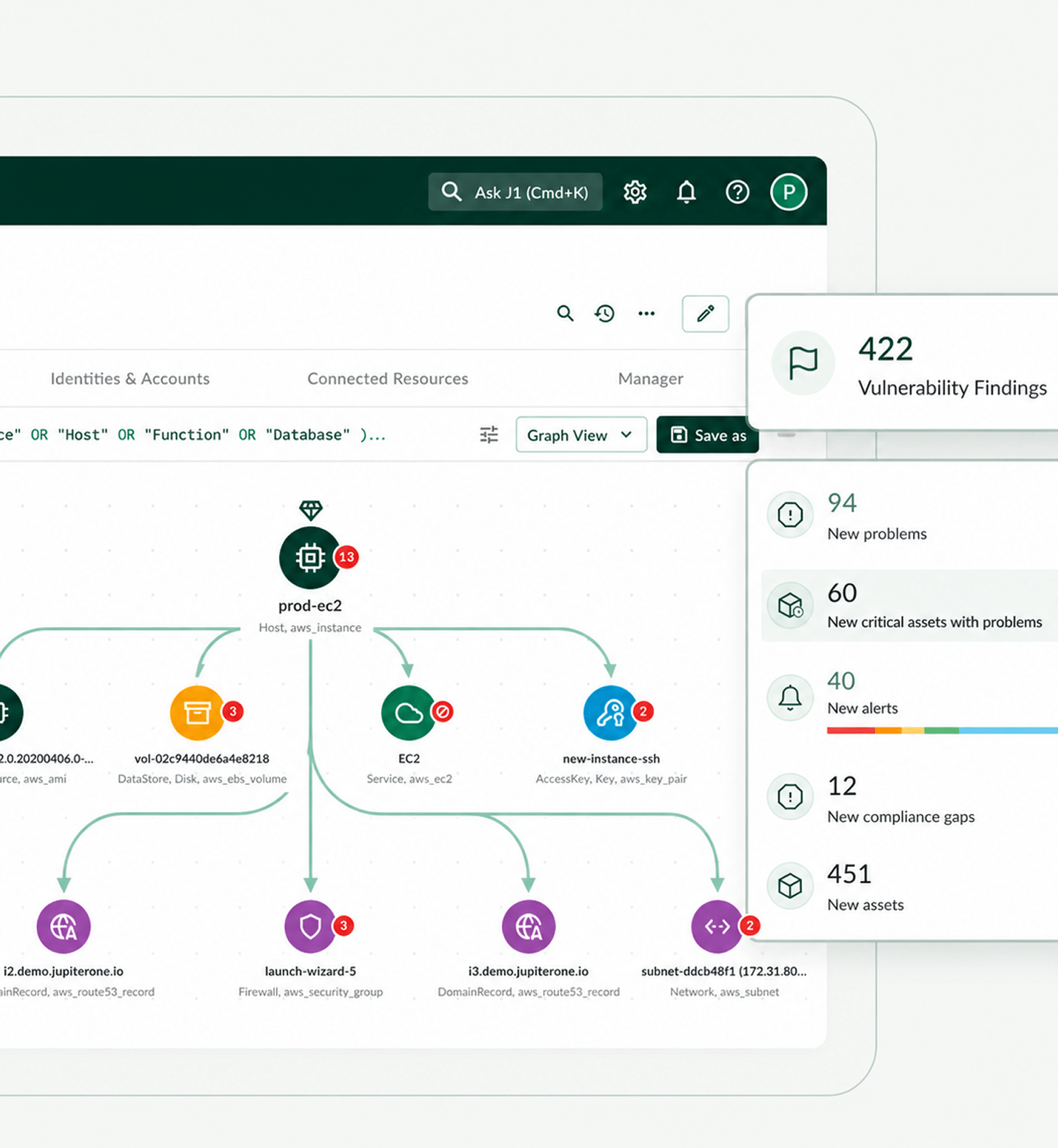
Map relationships
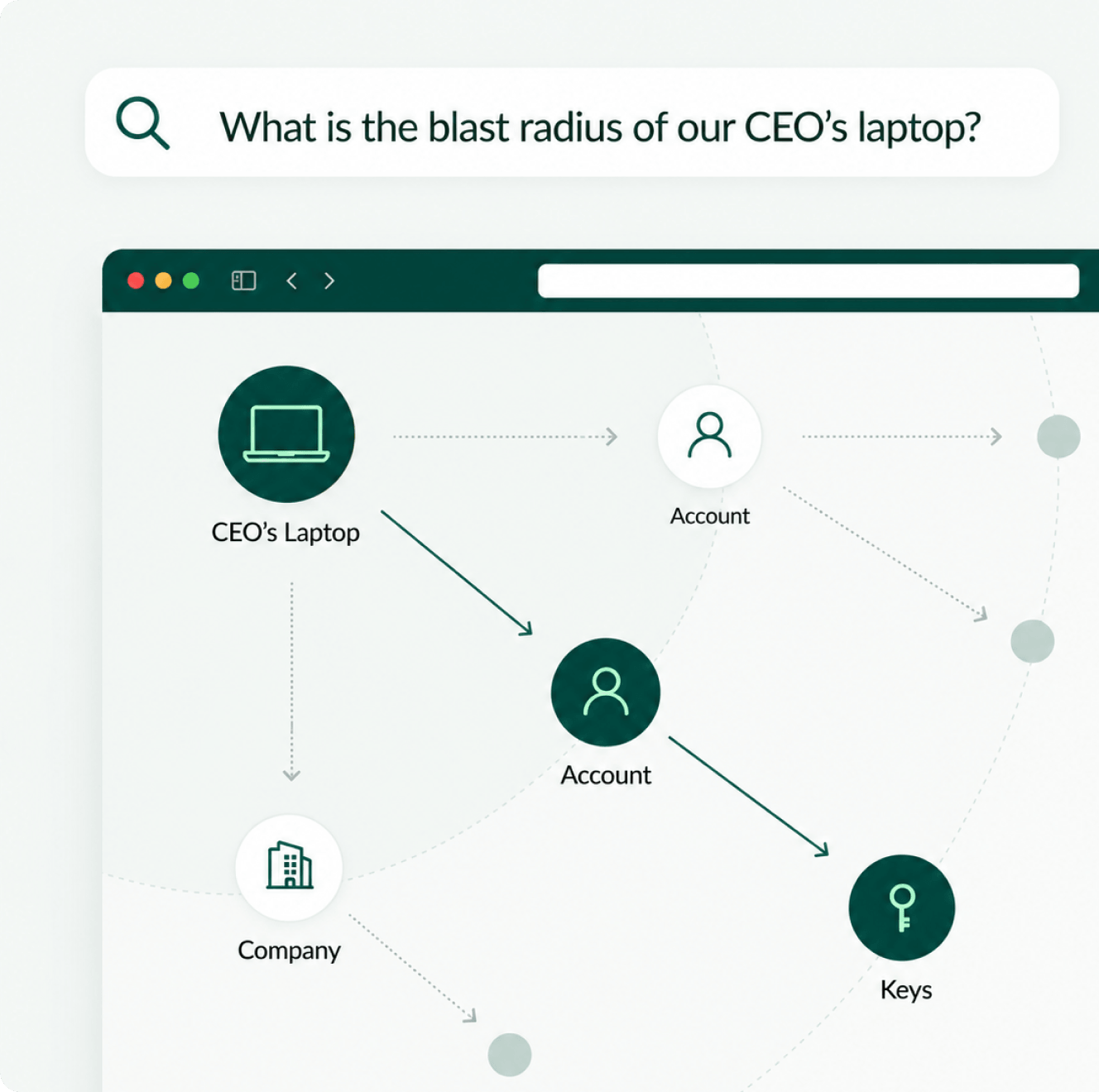
Visualize all the connections between your assets and uncover toxic combinations and hidden relationships that increase the risk of a material security incident.
See the blast radius of all the assets affected by security incidents. Detect downstream vulnerabilities.
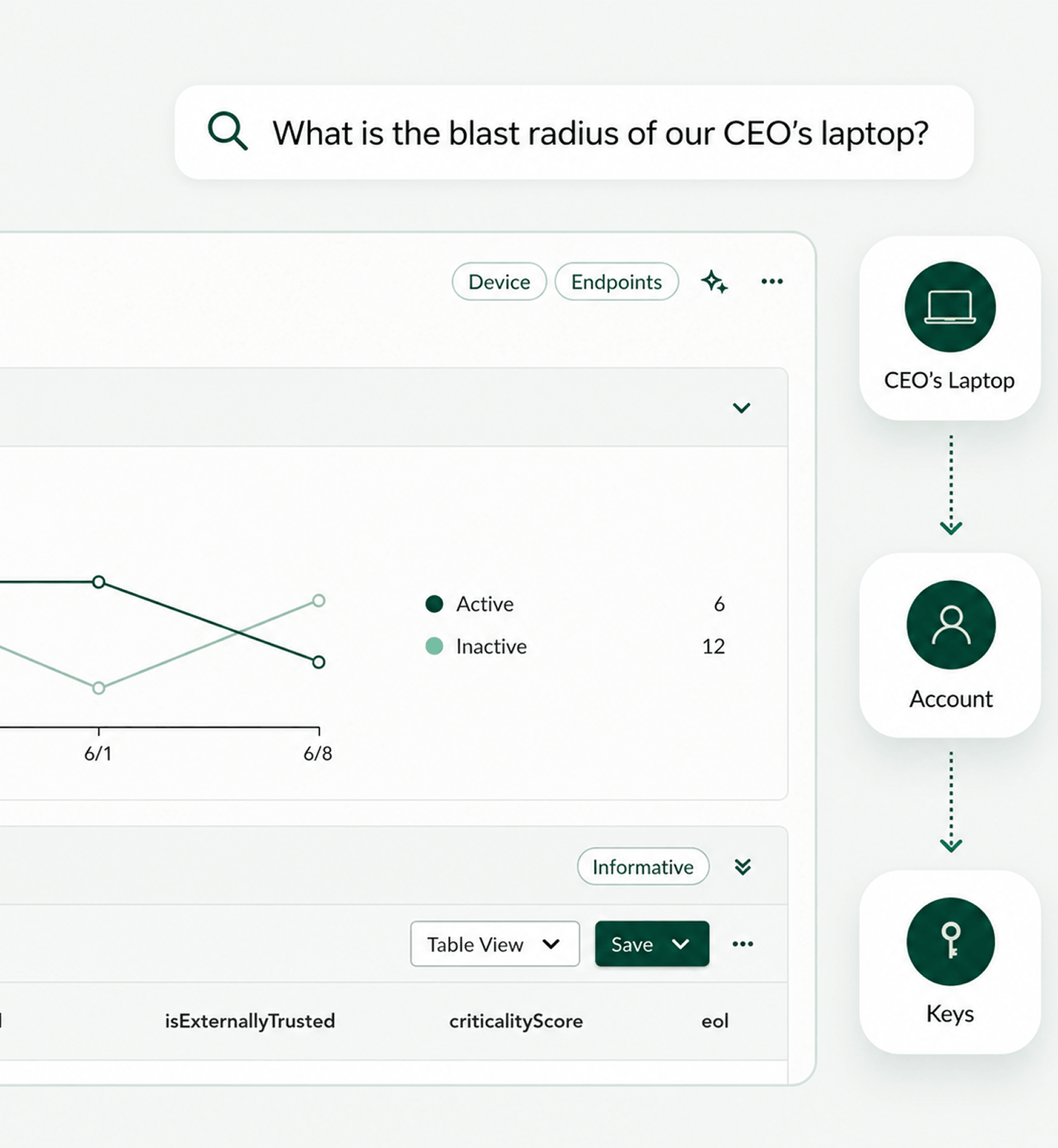
Query assets with natural language
Get detailed answers to any questions about your environment. Select queries from a pre-built library or create your own.
Quickly analyze your assets. Identify security gaps.
Report insights instantly
Turn raw data into actionable insights tailored to your needs.
Clear, intuitive visuals make it easy to quickly spot risks, track performance, and make informed decisions.


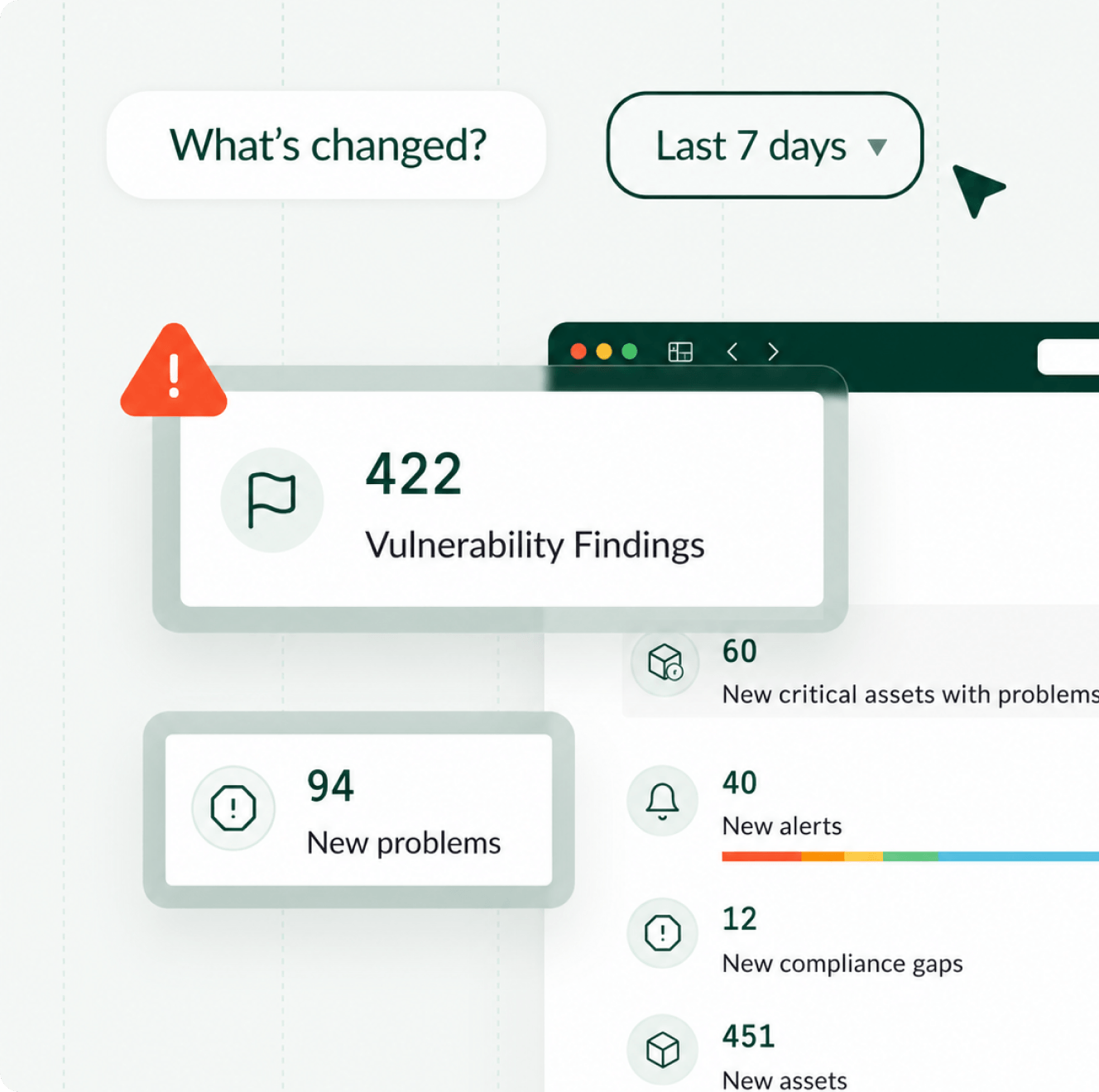
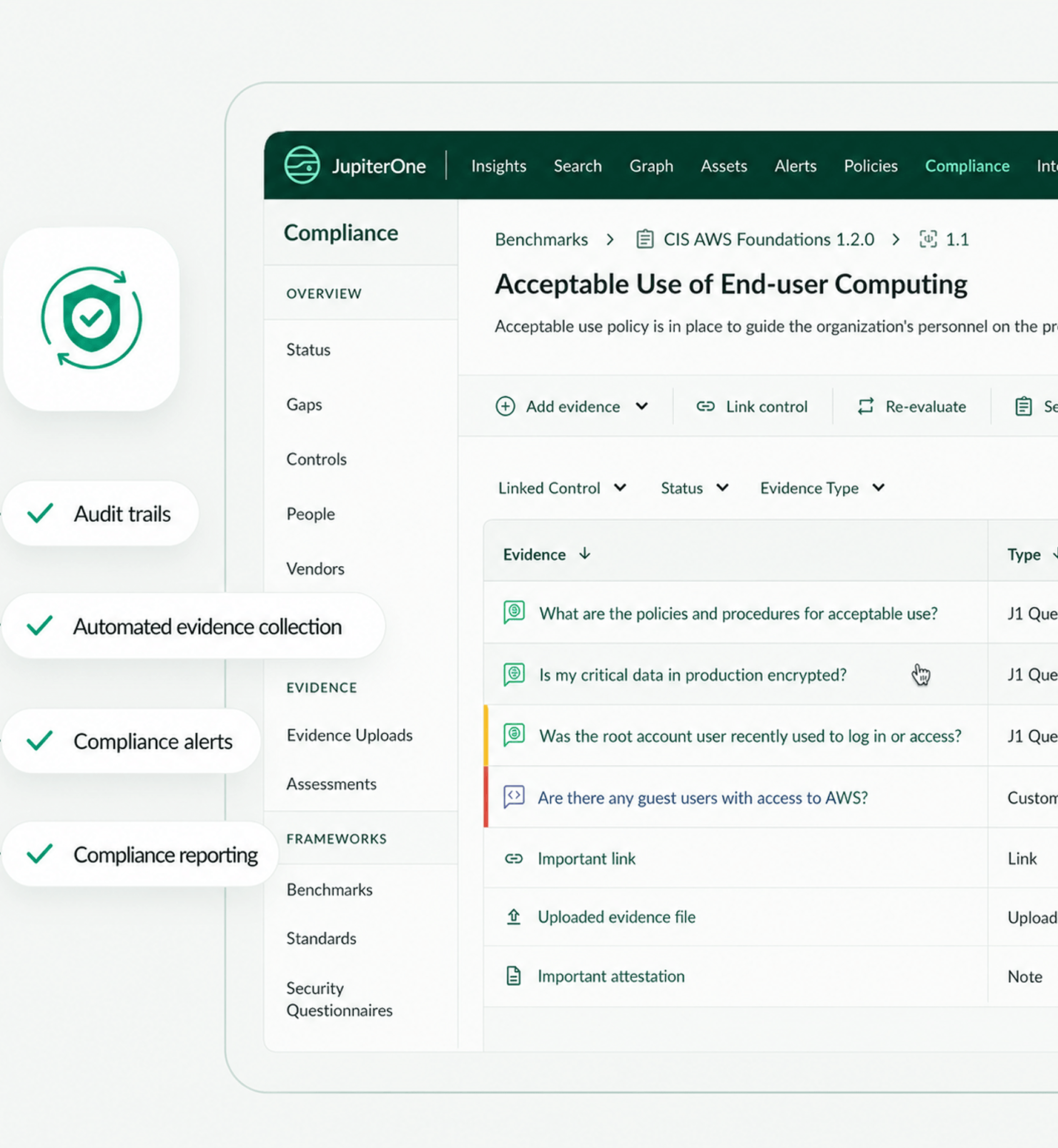
Automate workflows
Pre-built dashboards view important asset data at a glance. Customize with widgets based on your most frequently used queries. Proactively notify teams with built-in and custom alerts.
Know where to start investigations and reduce incident response times.
Get unified visibility into your entire cloud infrastructure
see all integrations
Salesforce
View more
Cloudflare
View more
Datadog
View more
AWS
View more
Snowflake
View more
Google Cloud
View more
Kubernetes Native
View more
Slack
View more
We’re here to answer all your questions
Can’t find what you’re looking for?
Send us an e-mail
What is an asset?
Cyber assets are the on-prem and cloud resources in a company's security and IT infrastructure: apps, data, code repos, devices, networks, policies, security controls, users, configurations, and more.
What are common use cases for JupiterOne?
Asset Management, Vulnerability Prioritization, Incident Response, and Compliance.
What tools does JupiterOne integrate with?
200+ security, IT, DevOps, and HR tools — AWS, Azure, Google, Snowflake, Salesforce, Jira, Qualys, Okta, GitHub, and more.
How do I use queries to monitor my environment?
Custom reports for security and compliance — pre-built queries or natural-language searches. Turn queries into triggers that alert teams of critical changes.
Prioritize with confidence with complete asset management and analysis.
Copyright © JupiterOne 2026. All rights reserved.